If you haven’t already, be sure to check out Part I and Part II.
In this third installment, we’ll look at what you will find when you first turn on the Juniper SRX Series Security Services Gateway and to get you through some initial configuration. Be reminded that, as we discussed in one of the previous articles, the SRX I’m using was sold by Dell with the Dell Logo on the device and in the software. Dell once sold the SRX as the PowerConnect J-SRX Series. Therefore, while I fully expect there to be some differences between what I have and what you have (one not sold by Dell), I do expect them to be minimal.
When you first power on the SRX, the first port is usually defaulted to be the port you connect to your ISP. The other ports are arranged into switching ports all on the same vLAN. DHCP is turned on and will start giving out IP addresses in the 192.168.1.x range. As you may have guessed by now, the default IP address of the SRX is 192.168.1.1.
While I did mention that we will not be concerned with the Graphical User Interface of the SRX, it is the fastest way to get the machine initially configured. If you are going to use Internet Explorer, be sure to put the address 192.168.1.1 in your trusted sites and make certain the trusted sites security setting is set to low. Otherwise, much of the SRX website (referred to by Juniper as J-Web) will not work. Below is the initial logon screen.
Do remember that you will not see the Dell logo or references to Dell if your SRX is not branded by and resold by Dell. The default username is root and the default password is blank. The root user is the super user of the SRX, and that shows off the SRX’s Unix heritage. Once you log on the first time, you’ll see the initial setup screen.
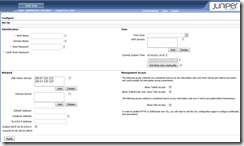
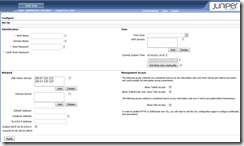
From here you can fill in some basic information to get the device working. Here are the values I’m entering:
- Host Name: I set this to “Juniper”. You may call the device anything you wish to distinguish it on your network.
- Domain Name: I leave this blank.
- Root Password: Of course, having a blank password is NEVER a good idea. There are no restrictions on the password, so it is your responsibility to choose something strong.
- Verify Root Password: What is says.
- DNS Name Servers: Replace these with the ones assigned by your ISP.
- Domain Search: Leave blank
- Default Gateway: Provided by your ISP.
- Loopback Address: Leave Blank
- fe-0/0/0.0 Address: If you have an SRX210, this field may read ge-0/0/0.0 Address depending on what kind of interface you have. If you are going to get addresses assigned by your ISP via DHCP, leave this field blank. Otherwise, fill in your static IP address here.
- Enable DHCP on fe-0/0/0.0: If you have an SRX210, this field may read ge-0/0/0.0 Address depending on what kind of interface you have. If you are going to get addresses assigned by your ISP via DHCP, check this box. Otherwise, make sure it is unchecked.
- Time Zone: Pretty obvious, those I have never cared for this particular way of choosing time zones. Why can’t people just use Eastern Standard, Pacific, Central, Mountain, etc.? Finding the closes city that matches yours is a pain sometimes.
- NTP Servers: Fill these in if you so desire.
- Allow Telnet Access: Make sure this is checked. The majority of examples I give will be using Telnet as the way to connect to the device.
- Allow JUNOScript over Clear-Text Access: Uncheck this.
- Allow SSH Access: Make sure this is checked. We may use it later.
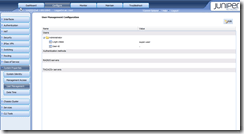
Now click Apply and wait for a few moments. Once you are done, you’ll see a dashboard like this one:
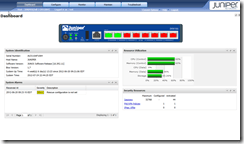
This dashboard is fairly useful if you want to get a quick estimate of machine condition. The first thing we need to do is create a new user to use other than the all powerful root. Go ahead and click on the CONFIGURE tab at the top, then on the left menu that appears click on SYSTEM PROPERTIES and under that click USER MANAGEMENT. You should now see something like this:
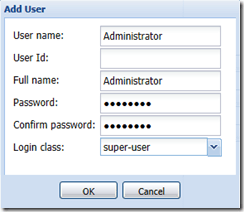
In the upper-right hand corner, click the Edit button. In the new window that appears, click Add. In the Add-User field, fill out the User Name, Full Name, Password, and Confirm Password fields. Choose Super-User as the login class. Don’t worry about the User ID field as it is not required. Your entry should look something like this:
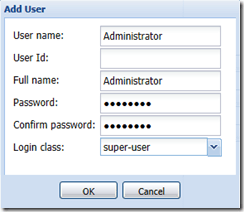
Notice I called my new user Administrator. First, I’m a Windows guy. Get used to it.  Second, usernames are Case Sensitive. Keep that in mind regarding the SRX. Go ahead and click OK all the way out until you see the SRX validate your settings and then the prompt telling you that you have to commit your changes. You’ll find the Commit Options button at the top under the Troubleshoot tab. On that menu, click Commit. You’ll then see a Configuration Delivery progress window appear. Once that window goes away, you’ll see the user you just created.
Second, usernames are Case Sensitive. Keep that in mind regarding the SRX. Go ahead and click OK all the way out until you see the SRX validate your settings and then the prompt telling you that you have to commit your changes. You’ll find the Commit Options button at the top under the Troubleshoot tab. On that menu, click Commit. You’ll then see a Configuration Delivery progress window appear. Once that window goes away, you’ll see the user you just created.
You can go ahead and close the J-Web user interface. It is doubtful we will ever use it again. You can probably see why just by the “clunky” feel it has.
Once you are done with these initial settings, you should now have Internet access with your new SRX. In the next post, I’ll go over the default security settings the SRX puts in place for you. After that, another brief technical over view on interface types and things like that. We will then be done with our quick intro series on the Juniper SRX Series Security Services Gateway and will be ready for more serious material.
James