By default, the Juniper SRX100 and SRX210 set up fe-0/0/0 as your Internet connection interface and the rest of the interfaces (fe-0/0/1 – fe-0/0/7 on the SRX100) as switching ports on a single vLAN. It is not uncommon for a network to require more than one vLAN for either political or technical reasons. For my home, in which I am using a SRX100, I have the reason in that I want my family computers on one vLAN and my Dell T310 server with all my test virtual machines on other vLANs. This way issues such as my test Small Business Server 2003 machine, with its own DHCP server, will not interfere with other computers which belong to my family (my wife has a mini-laptop, we also have an XBox). Furthermore, I could go further by setting up a Windows Server 2012 Essentials machine with its own DHCP server as well and it would not interfere with the SBS 2003 virtual machine nor the family machines. As long as everyone is on their own vLAN, all should be well.
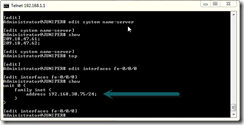
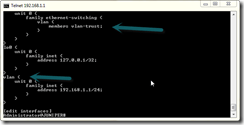
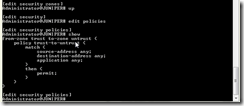
First, type in edit interfaces vlan in the SRX to get to the vLAN interface. Remember that each physical interface can have many logical interfaces. Obviously, the vlan interface is not a physical interface (it doesn’t represent a physical interface on the front of the machine) yet the same rule applies nonetheless. Type the following to create three more vLANs for this interface:
set unit 1 family inet address 192.168.5.1/24
set unit 2 family inet address 192.168.10.1/24
set unit 3 family inet address 192.168.15.1/24
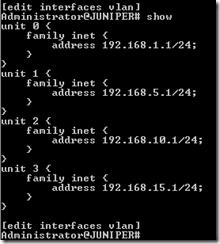
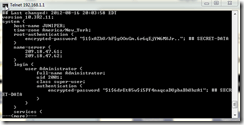
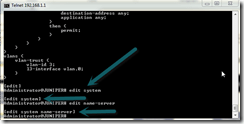
When you type show you should see the following for the current config of your vlan interface (note that unit 0 is the default that was already there):
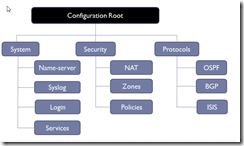
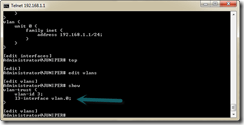
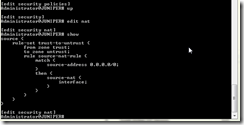
Now, we need to go to the actual vlan settings of the SRX. Type top to get out of interfaces and back to the top of the configuration tree, then type edit vlans. Type the following three set commands to create new vlans we will tie into our interface.
set vlan-trust2 vlan-id 4 l3-interface vlan.2
set vlan-trust3 vlan-id 5 l3-interface vlan.3
set vlan-trust4 vlan-id 6 l3-interface vlan.4
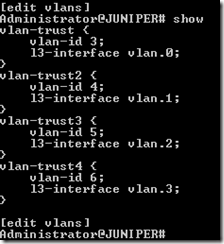
If you type show your configuration for vlans should now look like this:
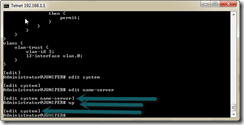
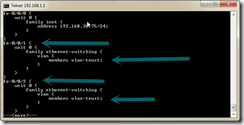
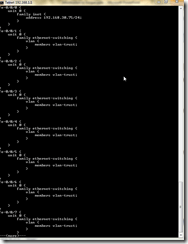
Now we must set three interfaces to our new vlans – one to each vlan. Type top to go to the top of the configuration tree and then type edit interfaces to get back in to the interface list. For my configuration, I’m going to assign fe-0/0/7 to my fourth vlan, fe-0/0/6 to my third vlan, and fe-0/0/5 to my second vlan. Type the following:
delete fe-0/0/7 unit 0 family ethernet-switching vlan members vlan-trust
set fe-0/0/7 unit 0 ethernet-switching vlan members vlan-trust4
delete fe-0/0/6 unit 0 family ethernet-switching vlan members vlan-trust
set fe-0/0/6 unit 0 ethernet-switching vlan members vlan-trust3
delete fe-0/0/5 unit 0 family ethernet-switching vlan members vlan-trust
set fe-0/0/5 unit 0 ethernet-switching vlan members vlan-trust2
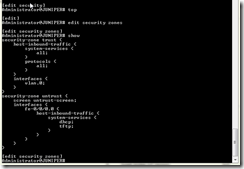
Our last step is to configure DHCP for one of the vlans. I need DHCP for only one of the vlans as the other two with have a server such as Windows Server 2012 Essentials as the DHCP server. Type top to make sure you are at the top of the configuration tree. Then type edit system services dhcp.
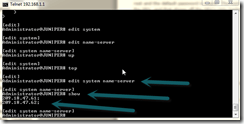
Type the following commands to create a new DHCP scope and assign it to the last vlan:
delete router
set pool 192.168.1.0/24 router 192.168.1.1
set pool 192.168.15.0/24 address-range low 192.168.15.10 high 192.168.15.254
set pool 192.168.15.0/24 router 192.168.15.1
set pool 192.168.15.0/24 propagate-settings fe-0/0/0
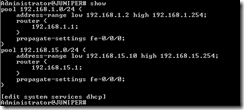
Notice we had to delete the original router entry since it was outside the scope of any given pool and, therefore, would have propagated that router setting out to all DHCP scopes. If you received an error typing that delete command, don’t worry, just type show to see where the router settings entry is. If is it already in the first first pool, then skip that command and finish setting up the second pool. After typing show your DHCP should look like this:
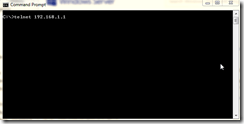
Once you are done with that, do a commit confirmed 5 which will commit your settings but give you 3 minutes to type confirmed again before rolling you back. This way, if a mistake is made, you will get back to your last known good configuration and can try again. While waiting your 5 minutes, be sure to connect a computer to the other interfaces on the device to see if they get connectivity. For those interfaces without DHCP, you’ll need to statically assign an IP address. Once you verify all is well, type commit again to make the changes permanent before you are rolled back.
We now have three vLANs on our SRX. One vLAN with interfaces fe-0/01 through fe-0/0/4 with DHCP, one at fe-0/0/5 without DHCP, one at fe-0/0/6 without DHCP, and one at fe-0/0/7 with DHCP. The table below summarizes.
|
vLAN |
Interface |
IP Address |
DHCP |
| 0 | fe-0/0/1 | 192.168.1.0/24 | Yes |
| fe-0/0/2 | 192.168.1.0/24 | ||
| fe-0/0/3 | 192.168.1.0/24 | ||
| fe-0/0/4 | 192.168.1.0/24 | ||
| 1 | fe-0/0/5 | 192.168.5.0/24 | No |
| 2 | fe-0/0/6 | 192.168.10.0/24 | No |
| 3 | fe-0/0/7 | 192.168.15.0/24 | Yes |
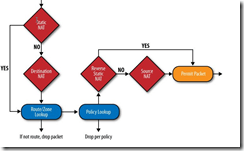
As far as security goes, all the vLANs belong to the trust zone and follow all the policies of that zone. Later on we will look at putting vLANs into their own zones so we can have more granular control over security.
JamesNT