In Part III of our quick start series, we went through the Juniper set up screens to set some initial configuration settings for our new device. Today, we are going to use the CLI to explorer the default configuration given to us by those initial configurations.
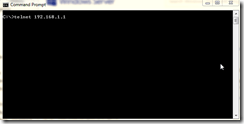
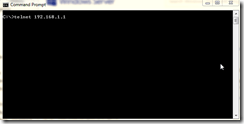
To access the SRX CLI, you need Telnet. Please note that on Windows 7 and Windows Server 2008 R2 the Telnet client is not installed by default. You may follow these instructions to install Telnet.
Once you have Telnet installed, if you needed to install it, open a command prompt and type TELNET 192.168.1.1.
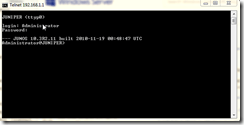
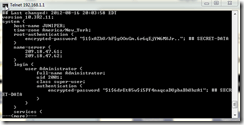
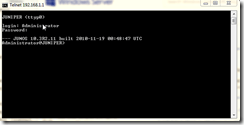
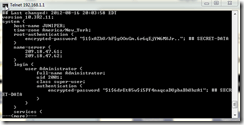
Once you hit enter, you will be presented with a username prompt. Use the Administrator account that we created in Part III of the Quick Start series to log in. Note that both user names and passwords are CASE SENSITIVE. Once logged in, you’ll see a prompt like this.
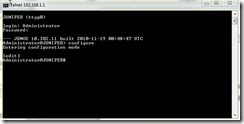
At the command prompt, type the word configure and press Enter to enter configuration mode. There are two modes to the SRX, we will investigate them both in future posts. Suffice to say the mode you enter into when first logging on is Operation Mode used for monitoring and the like. Configuration Mode is where you configure the device. Your prompt should now look like this.
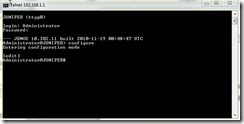
Notice that the prompt changed from using a “>” symbol to using a “#” symbol. The “#” symbol means you are in configuration mode. The “>” means Operational Mode.
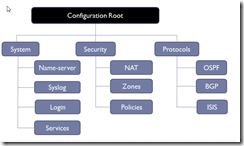
In Configuration Mode, there are certain commands you use to navigate the configuration tree. The following shows most, but not all, of the configuration tree:
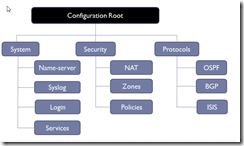
We will be investigating many of the parts of the configuration tree in future posts. To navigate the tree, we do have certain commands to use.
show – shows the configuration of the part of the tree you are at. If you are at the configuration root, the show command will show you the entire tree which can take a long time if there are lots of things configured. If, however, you have navigated to, say, System | Name-server then the show command will show you only what is in that section. If there is more information to show than what your window will allow, the show command will fill the window and stop until you press the spacebar for the next page. The percentage you have seen thus far is shown at the bottom.
edit – use this command to tell the CLI what part of the tree you wish to edit. For example, if you type edit system then you will enter the system stanza of the tree. Do notice that the prompt tells you were you are.
up – use this command to navigate up levels of the tree. edit brings you down to levels you specify, up brings you up the next level above where you are.
top – if you want to go straight up to the configuration root, use top.
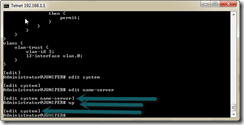
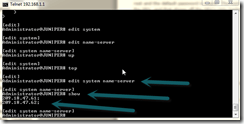
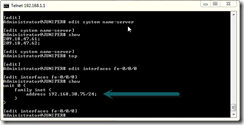
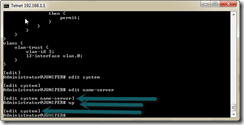
Now that we know how to move around a bit, let’s take a look at certain parts of the tree, called Stanzas. First, type the word top to make sure you are at the top of the configuration root in case you have been playing around. Next, type the following:
edit system name-server
This will place you in the System part of the tree in the name-server stanza. Now type show.
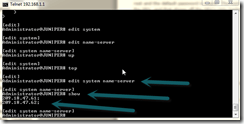
You should see the IP addresses of the name servers you typed in while following along in Part III of the quick intro. Type top to go back to the top of the configuration tree (refer to the diagram above when needed).
Now type the following commands:
edit interfaces fe-0/0/0
show
If you are using the SRX210, replace the fe with ge. Otherwise, you should see this:
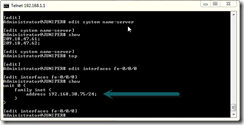
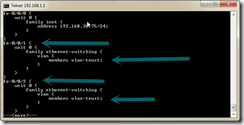
Notice where the arrow is pointing. If in the initial configuration screen you unchecked the DHCP box and entered a static IP, that IP is here. Otherwise, you’ll see DHCP. This interface is the one that should be plugged in to your ISP. In my case, it is plugged into my Linksys router which allows my other computers to get on the Internet as well. Later on, we are going to make some configuration changes to make the SRX my router for my network and we will remove the cheap Linksys. Type up to go up one level and then type show:
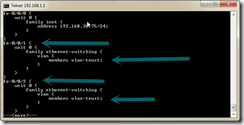
Notice that we are now looking at all the interfaces. The show command as I mentioned earlier shows you everything in the current position of the tree, including sub-branches of that position. Since we are at the interface level, it is showing us all the interfaces along with their configurations. Notice you have the —(more)— at the bottom for scrolling. Use the space bar to scroll on down.
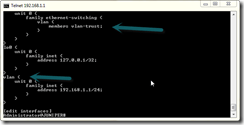
Notice also that while fe-0/0/0 is assigned a static IP address, or DHCP depending on your choice in the initial configuration screen, the other interfaces are all assigned to a VLAN. You also have interface lo0 which is, of course, the loopback adapter. At the bottom, you should see the interface for the VLAN and the IP address it is assigned which is the IP address range of your internal network with the SRX.
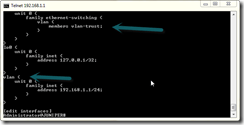
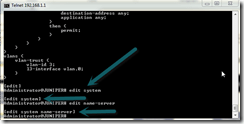
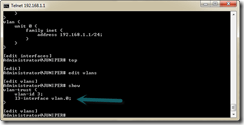
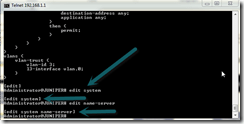
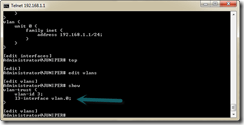
Let’s take a look a the VLAN itself. Type top to get to the configuration root. Then type:
edit vlans
show
Notice we have a Virtual LAN called “vlan-trust” defined and that the interface we saw above is assigned to it. Also, notice the shorthand for which unit to refer to. Instead of typing the name of the VLAN then the name of the unit, we just do vlan.0 where the zero is the unit. If you have more units, such as 10, 11, and 12, you could do vlan.10, vlan.11, vlan.12, etc.
So what we have is an logical interface that defines the IP address range of the VLAN, which is assigned to the VLAN itself, which is in turn assigned to the other interfaces (except fe-0/0/0). This allows us a great deal of flexibility. Think about. You could literally have each port on the front of the SRX assigned to a completely independent VLAN. Let us continue. Type top to get to the configuration root again. Now type the following:
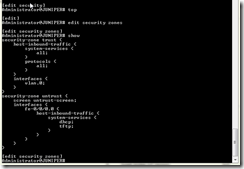
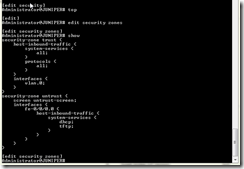
edit security zones
show
We are now looking at the default zones created by the SRX. One is called trust and the other is called untrust. Typically, trust is your internal LAN and untrust is the Internet. Notice what we are doing:
- For inbound traffic to the trust zone, we are pretty much allowing everything to go to the SRX. All protocols. And we assigned our VLAN, vlan.0, to this zone.
- For the untrust zone, we assigned fe-0/0/0 and notice that we allow only dhcp and tftp. Normally I remove these. Do keep in mind that if you remove DHCP and you chose DHCP as the way for fe-0/0/0 to get IP address from the ISP, you will no longer be able to get on the Internet should your ISP change IP addresses on you (assuming you don’t have a static address).
This all should make sense. fe-0/0/0 is plugged into our Internet connection and our vlan.0 is our internal network as we examined earlier. Although, in a true production environment we may place more limitations than this even on the Internal network instead of just allowing everything.
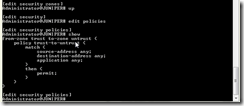
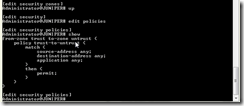
At the CLI prompt, type up to go up one level the type edit policies then type show.
We are now looking at our one and only default security policy. Should be pretty straight forward. We have one policy called “trust-to-untrust” that pretty much allows anything from the internal network to go out to the Internet. Since there is no policy allowing traffic from the Internet to the internal LAN, that means anything from the Internet is blocked.
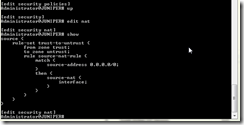
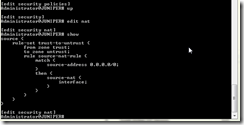
Type up one more time then type edit nat then type show. We are now looking at our Network Address Configuration. We have one rule translating addresses for traffic that goes out regardless of IP address. We do not translate any traffic coming to us since, thanks to our policy, we have no traffic coming in.
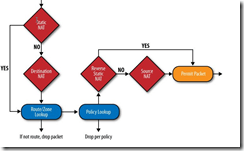
So what we have is this:
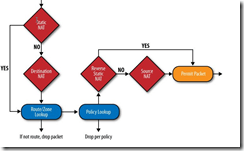
This is straight from the book I recommend on my Books I’m Reading page for learning the Juniper SRX Security Services Gateway. This diagram gives a decent idea of how traffic is processed by the SRX.
And this is the default configuration you are given after completing the initial setup wizard.
To exit the CLI of the Juniper SRX, type the exit command until your telnet session is closed.
Next up, we are going to add some VLANs and assign other ports to them. In my home network, I have my wife’s computer which will go on one VLAN, my computer which will go on another, and a Dell PowerEdge T310 server running several virtual machines that will all be on yet another VLAN.
Do keep in mind that my quick overviews and instructions on how to perform certain tasks are meant to show you how I’m using the SRX. If you really wish to learn the device properly, I recommend the book Junos Security found here at Amazon.com for paper back or you can go Kindle edition.
JamesNT